Friday, May 12, 2017, wasn’t a good day to be rushed to the hospital via ambulance in the UK. It also wasn’t a great day if you worked in the interior ministry in the Kremlin, if you were FedEx, or if your name was Marcus Hutchins, the cybersecurity-dude-turned-hero who tried unsuccessfully to stay out of the paparazzi limelight after saving the day.
The reason for all these bad days was because of WCry, also called WannaCry, a piece of ransomware that infected computers running Windows 7 across the globe, running an exploit in an unpatched version of Microsoft’s uber-popular but super-vulnerable operating system.
Effects ranged from taking down the UK’s National Health Service (and having ambulances rerouted, surgeries rescheduled, and doctors locked out of their electronic health record systems), to locking up Kremlin computers, to disrupting FedEx’s logistics — all with the threat to pay $300-$600 in Bitcoin to the ransomware authors to decrypt a user’s files.

People across the world saw this on May 12, telling them they “have not so enough time” [sic] to pay the bitcoin or have their files encrypted indefinitely.
Fortunately, Hutchins, a 22-year old cybersecurity researcher who works for Kryptos Logics, a Los Angeles-based cybersecurity firm, found a built-in killswitch in the ransomware wherein a previously unregistered domain would stop the spread of the virus when registered (it didn’t help computers that had already been affected, however.)
So where does DevOps fit in?
DevOps, though its name suggests just development and operations, also includes two other highly skilled IT professions: QA and security operations. We’ll focus on security operations here.
IT security isn’t anything new. Everything from major corporations to garage-dwelling tech startups have had information security workers keeping things locked tight for decades. What DevOps is doing, however, is turning IT security on its head, making it more agile, lean, and flexible. After all, security operations hasn’t been known to possess these character traits until recently.
That’s where Marcus Hutchins and his employer Kryptos Logics comes in. Hutchins was just working in his bedroom when he discovered the killswitch in WannaCry. But his role and his company reveal an important milestone in DevOps. Without security researchers working for organizations, they are left vulnerable and at the whim of OS and other software makers that put those companies at risk.
You may be wondering, “Shouldn’t viruses, trojans, and other malware threats be the responsibility of OS makers like Microsoft, RedHat, and the like?”
It’s true that Microsoft had a large part in the WannaCry exploit because they are responsible for making their operating systems safe. But Microsoft did push out a critical security patch in March that prevented the attack — for organizations that were agile enough to have deployed it already. However, organizations without the agile DevOps practices (such as Telefónica in Spain), which are needed to fast track security updates to prevent problems like WannaCry, left hundreds of thousands of computers vulnerable (230,000 to be more accurate) in organizations across the world.
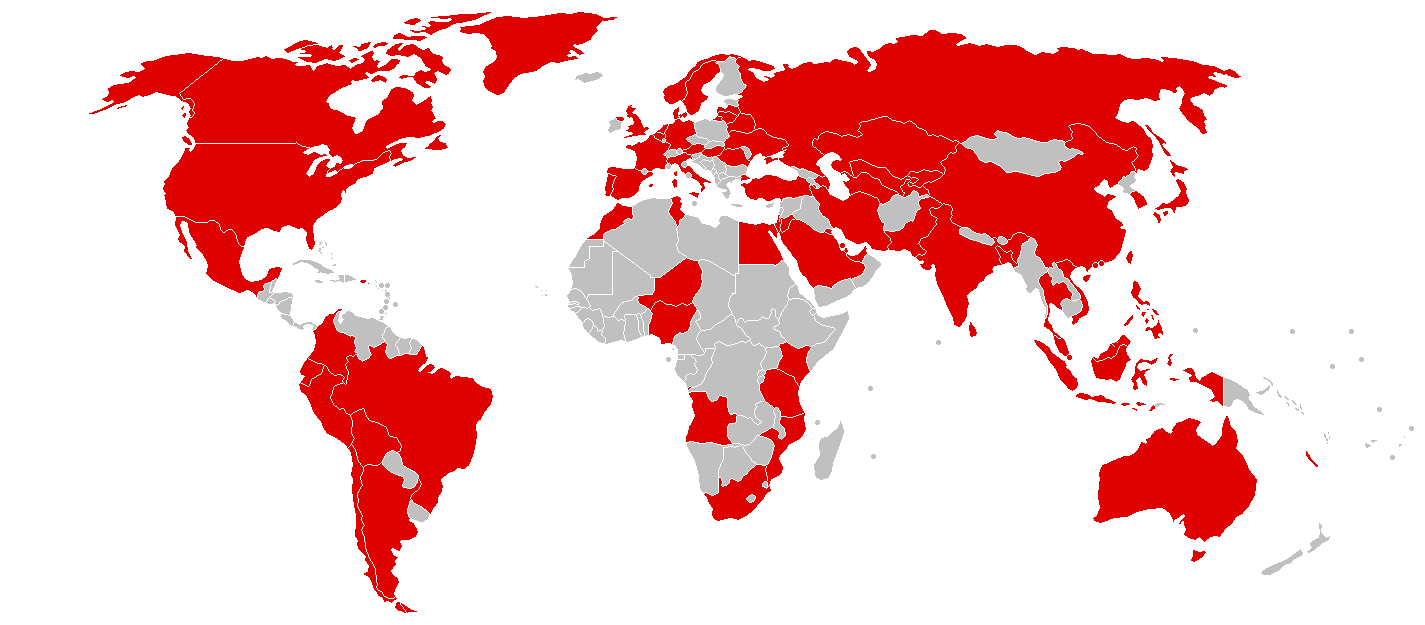
More than 230,000 computers in more than 150 countries across the world were initially hit by the WannaCry ransomware worm.
Source: Wikipedia
Make no mistake. This isn’t just an “IT problem” or “something the computer nerds at the company” are responsible for. Preventing malware on system-critical hardware is a DevOps process. Ultimately, the protection of each company comes down to its own responsibility. And within each company, that responsibility falls on its DevOps security team, the group of people (or person, as is usually the case in a small-to-medium business) working in the background to make sure its servers and apps are running, anticipating problems ahead of time, and using their platform of tools as best they can monitor cloud usage and threats, and proactively fight back as much as possible.
WannaCry isn’t over. EternalRocks is WannaCry’s “Scarier Successor,” we’re warned. Ransomware reached a peak last year and is predicted to remain the top cyber threat in 2017. The need for DevOps-focused security practices that allow an organization to pivot on its feet and respond to cyber threats is essential in the 2017-and-beyond landscape.
To protect your company, adopt agile DevOps security processes, build a platform of monitoring tools that suits your needs, and automate, automate, automate.




